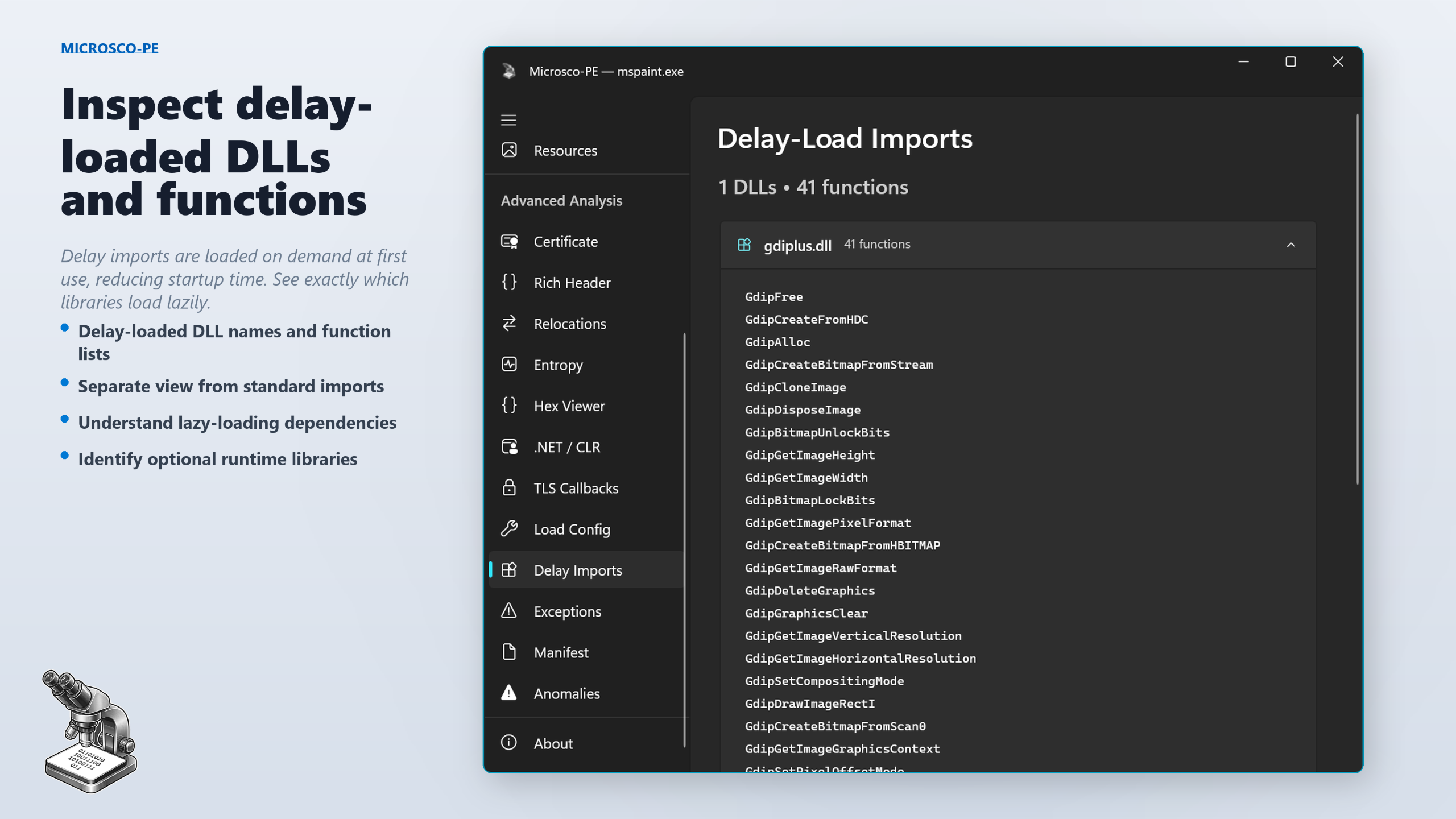
Microsco-PE
Modern Portable Executable Analyzer for Windows
Drag, drop, and explore every detail of any PE file — headers, imports, certificates, entropy, and 20 analysis views.
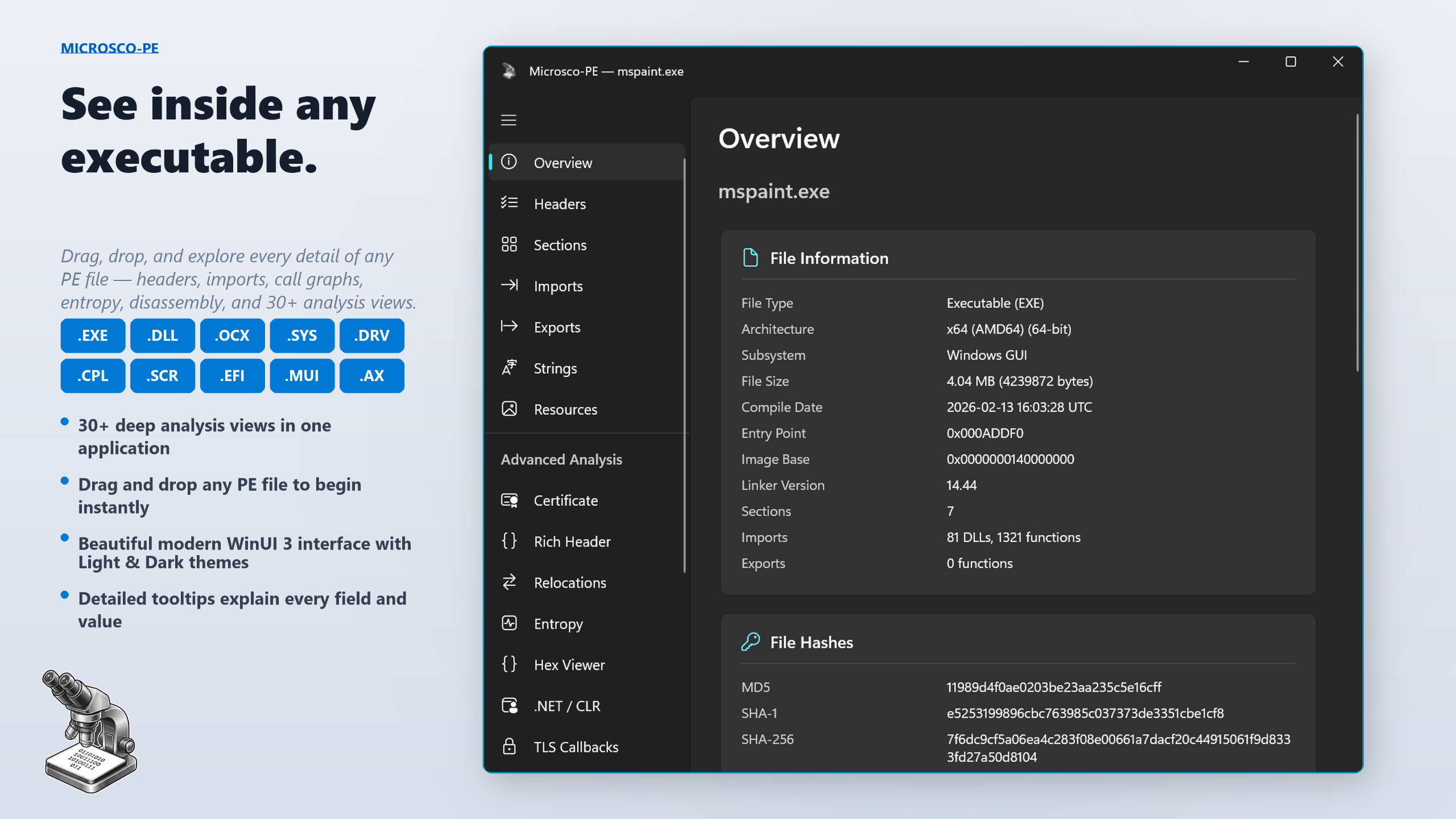
See inside any executable
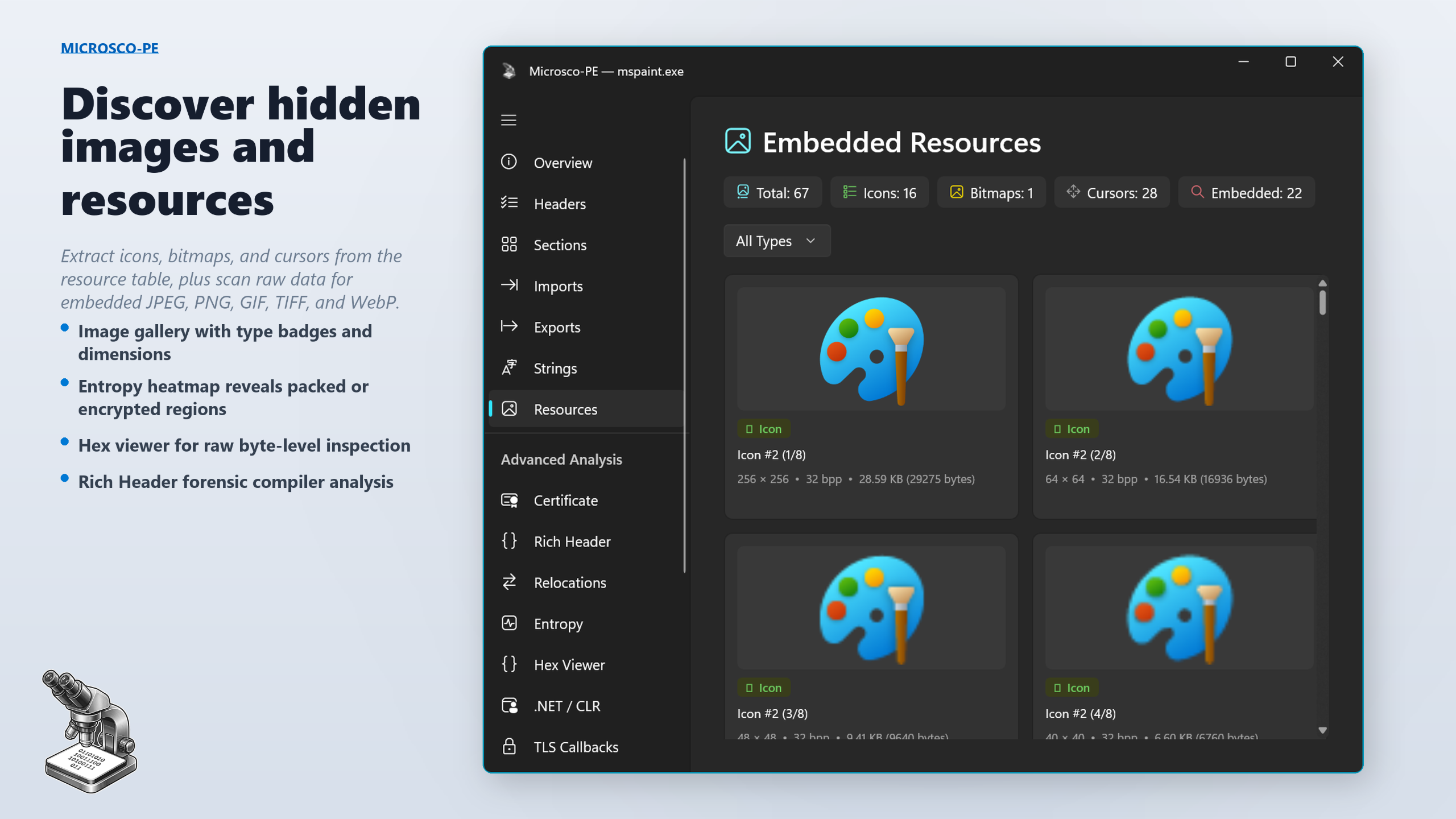
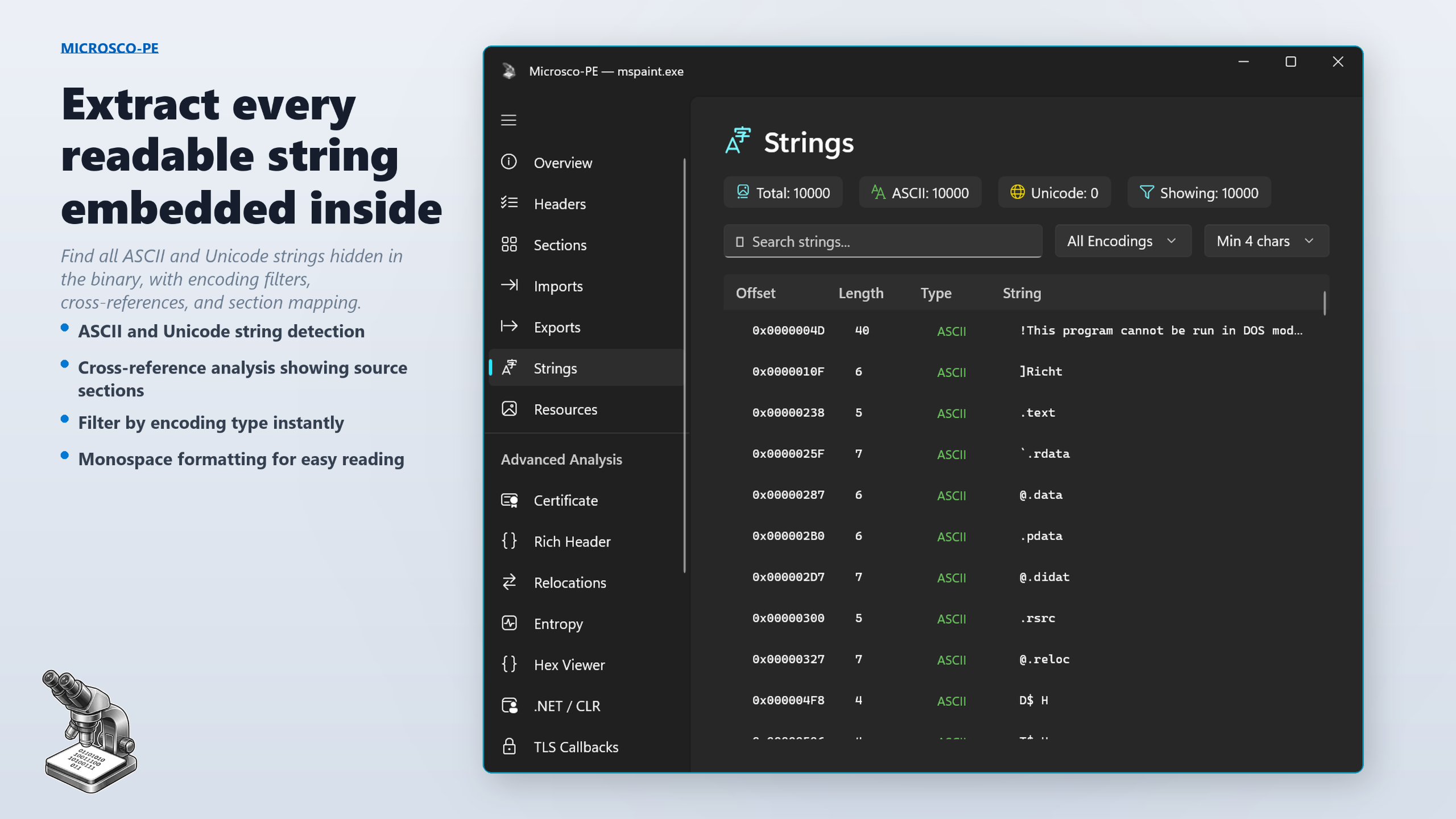
Portable Executable files power every application, driver, and library on Windows — but their internals are opaque to most tools. Microsco-PE opens them up. Drop any .exe, .dll, .sys, or .ocx onto the window and instantly explore headers, imports, exports, digital signatures, entropy, embedded resources, and much more.
Whether you are a security researcher, malware analyst, software developer, or simply curious about how Windows binaries work, Microsco-PE gives you deep, instant insight with a stunning modern interface.
20 analysis views, one application
How it works
See it in action
Built for people who take binaries seriously
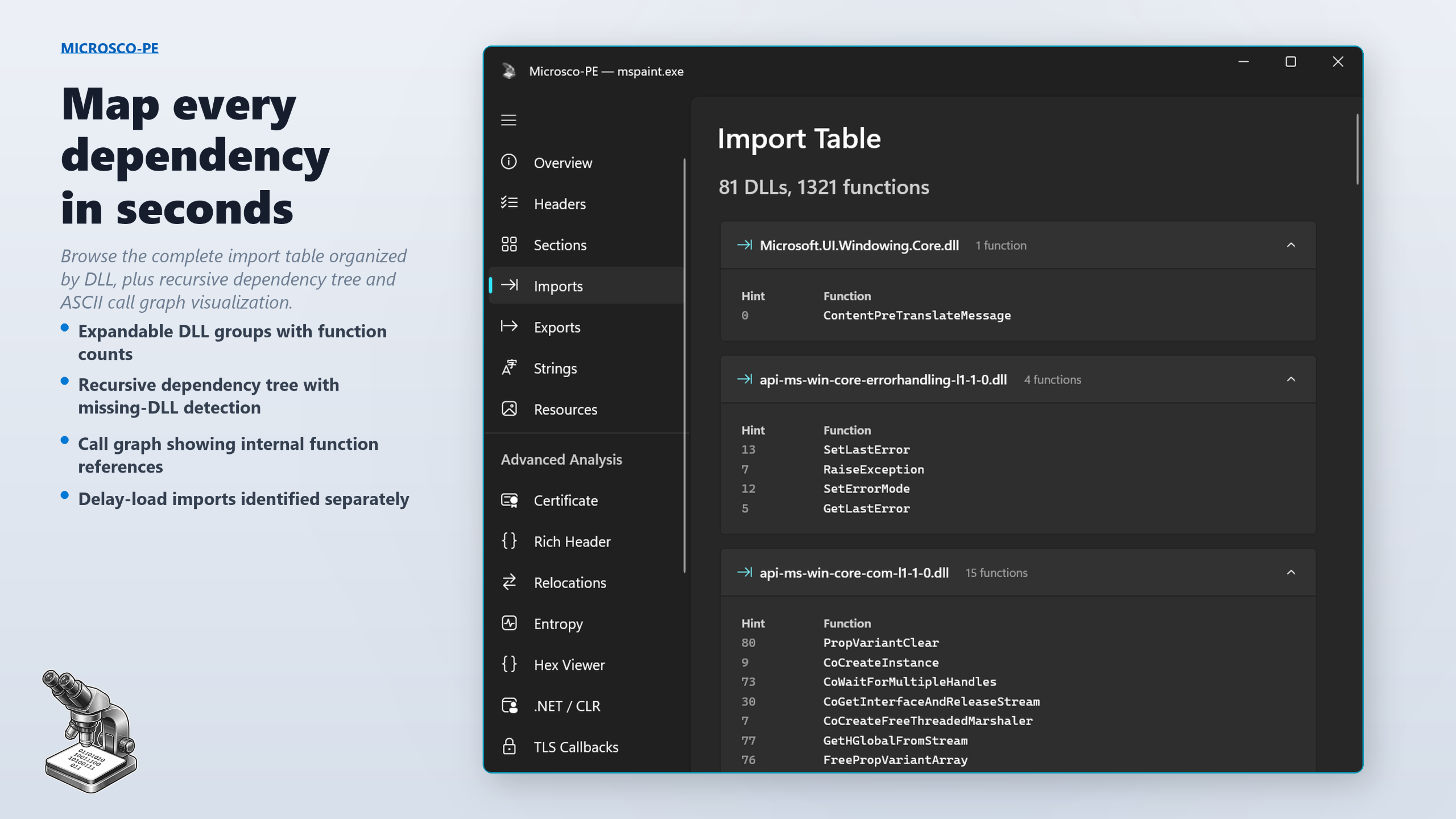
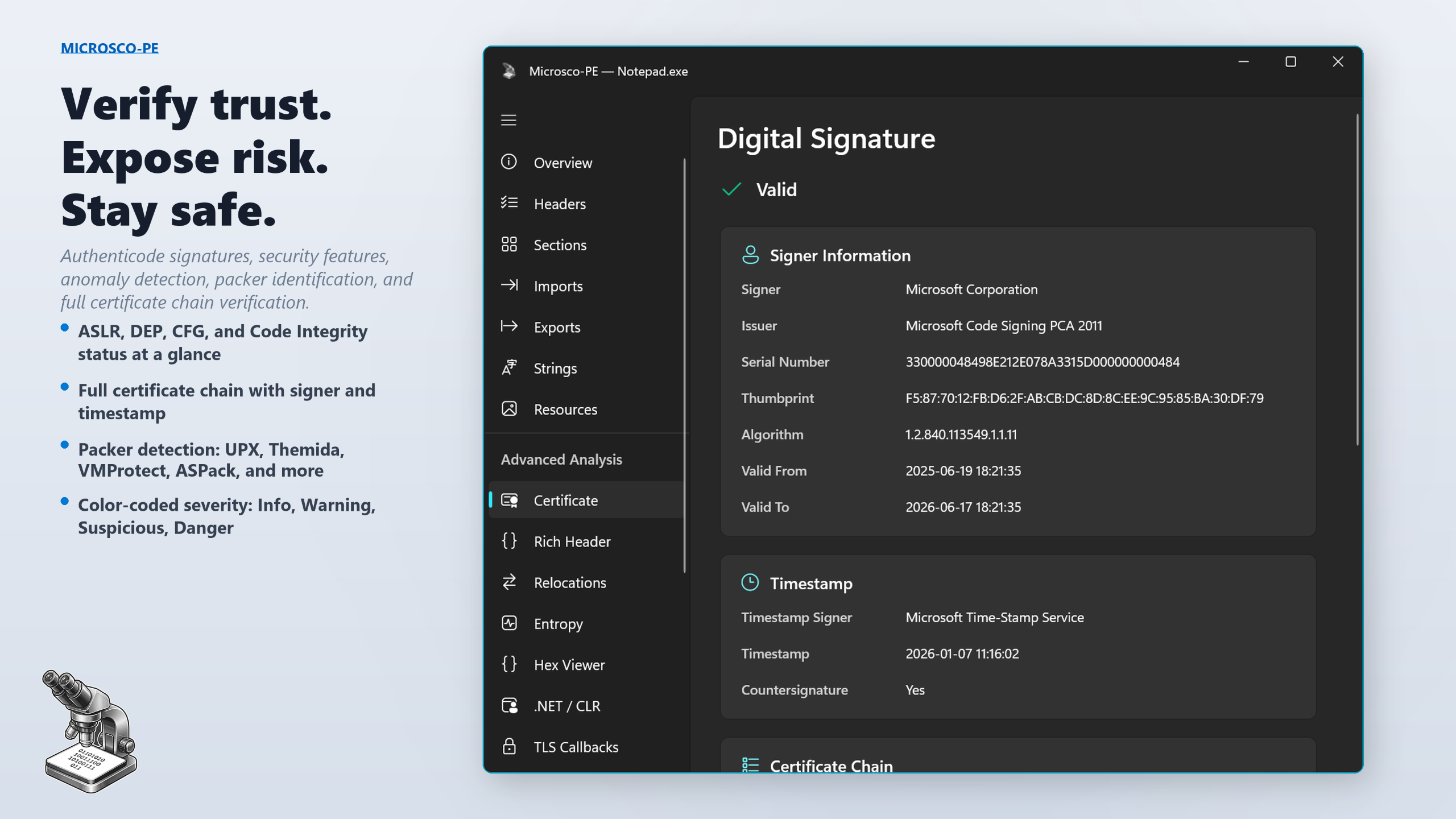
- Security researchers — verify signatures, inspect anomalies, and assess a binary’s security posture in seconds.
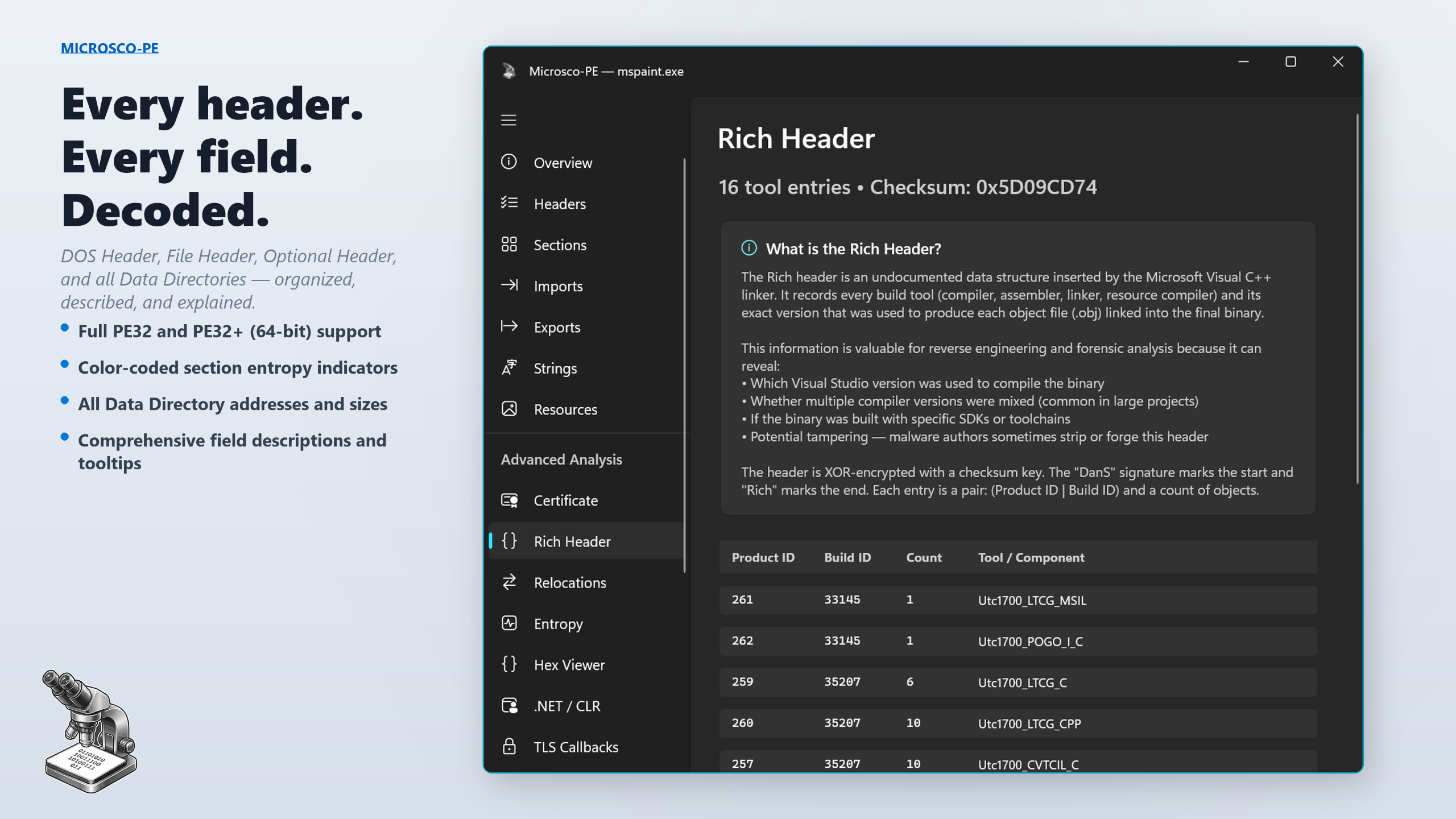
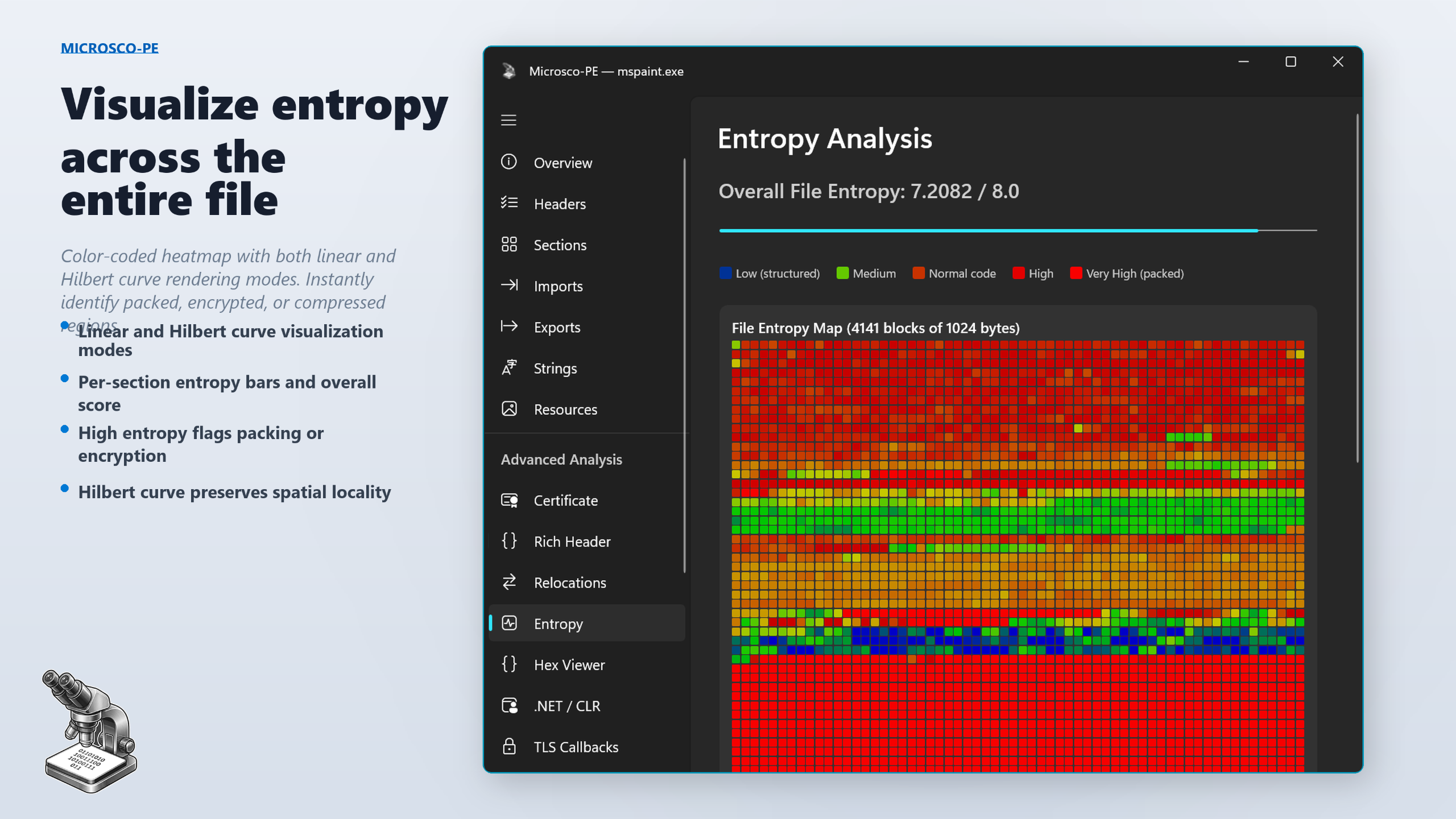
- Malware analysts — Rich header forensics, TLS callbacks, entropy heatmaps, and anomaly detection help triage samples fast.
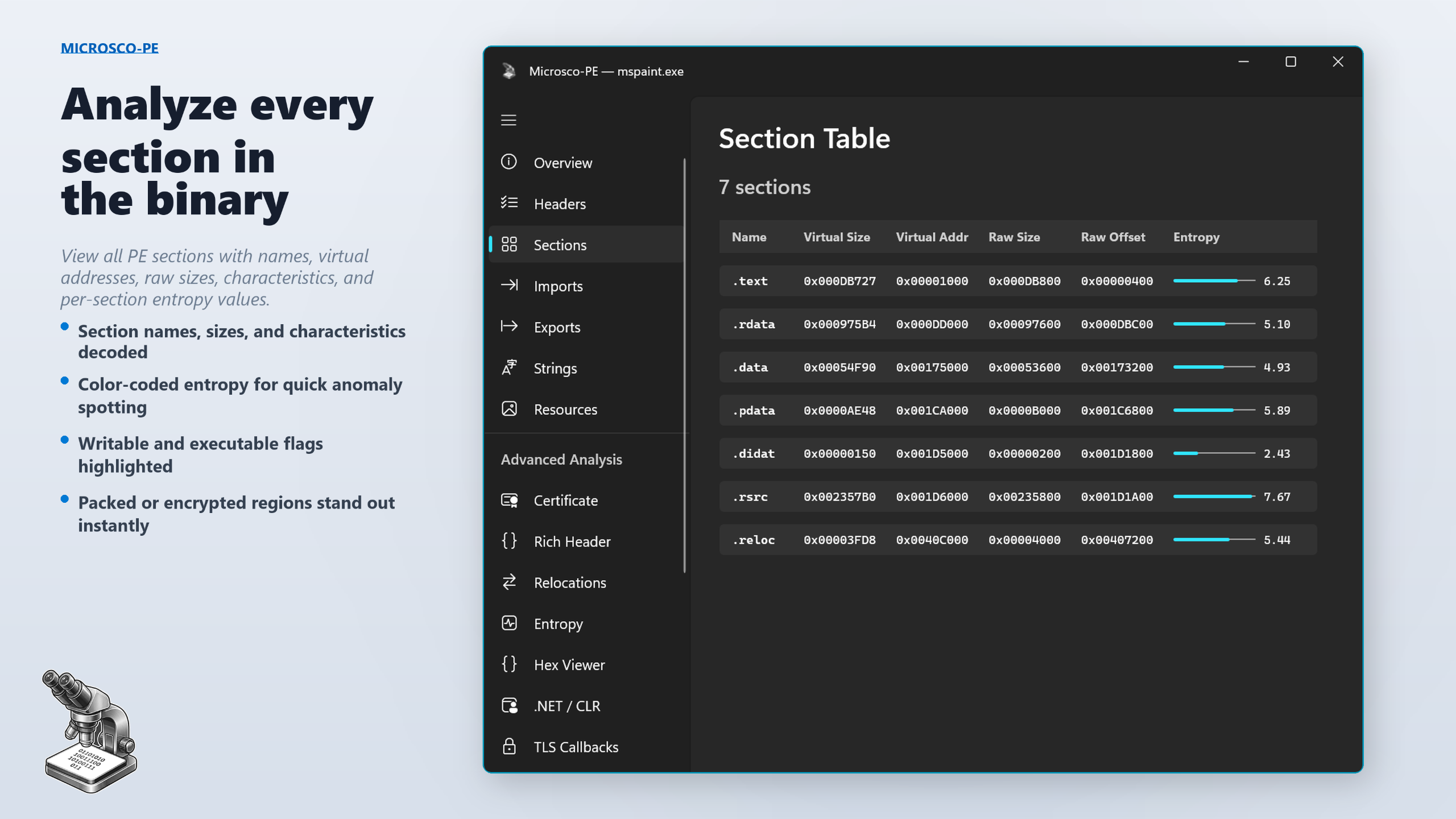
- Software developers — check your own builds for correct imports, exports, sections, and security flags before shipping.
- Reverse engineers — every header field decoded, every data directory mapped, every string extracted.
- Students & educators — detailed tooltips on every field make Microsco-PE the best way to learn the PE format.
Supported file types
- .exe — Windows Executables
- .dll — Dynamic Link Libraries
- .ocx — ActiveX / OLE Control Extensions
- .sys — System & Kernel Drivers
- .drv — Device Drivers
- .cpl — Control Panel Applets
- .scr — Screensavers
- .efi — EFI Applications & Drivers
- .mui — Multilingual User Interface Resources
- .tsp — Telephony Service Providers
- .ax — DirectShow Filters
Technical details
- Platform: Windows 10 and Windows 11
- Architecture: x64
- Interface: Modern WinUI 3 with Fluent Design
- Performance: Native C++ — files parse in milliseconds
- I/O: Memory-mapped file I/O for efficient large file handling
- PE support: Full 32-bit (PE32) and 64-bit (PE32+)
- Signing: Authenticode signature verification via WinVerifyTrust
- Hashing: BCrypt-based MD5, SHA-1, and SHA-256
- Privacy: Runs entirely on your machine. No uploads, no cloud, no tracking.
- Dependencies: Zero external dependencies — pure Windows SDK
Stop guessing. Start analyzing.
Support
Email: support@barkersoftware.com
